Students looking to access Duke’s online services and portals are now required to input a second form of verification—such as a code sent to a mobile phone or tablet—in addition to their NetID and password.
The result? Hacking the University’s system just got a lot more difficult, says Duke's Office of Information Technology.
Beginning April 17, the University mandated that all students use multi-factor authentication to log in to Duke services, including Sakai, DukeHub and their Duke inbox. Richard Biever, chief information security officer and director of identity management, said the change was a smart move for the University, which has had to ward off an increasing number of hacking and phishing attempts in recent years.
“When we are looking at security, we are looking at two things—we are looking at how do we protect the community and how do we detect when attacks occur and when they succeed,” Biever said. “The protection piece was multi-factor authentication.”
Biever said cybersecurity is crucial at major universities, where computer networks store a wide range of sensitive information related to research, resources and people.
He noted that his office locks approximately 100 accounts belonging to students, faculty or staff per month.
“This past January, it was over 200 due to a major set of phishing attacks,” Biever said.
Phishing is the practice of sending fraudulent electronic communications from supposedly trustworthy organizations in order to steal individuals' financial or personal information.
January’s hackers successfully phished faculty, staff and students and used their access to study the University’s account-security practices for future break-ins, Biever explained. They also used hacked student accounts to attack other schools from the University’s network space and send out more fraudulent emails.
Moreover, January’s attacks were not the first to strike the University. In 2013, shortly after the OIT Security Office began implementing multi-factor authentication for some members of the campus community, Duke faculty were hit with a direct deposit phishing attack. Several faculty members received an email promising a raise and asking that they follow a link.
“We had several faculty members that fell for it,” Biever said. “The attackers grabbed their NetID and password, logged in to [the University system], and then changed their bank account information so that their monthly paychecks got routed [overseas].”
Since that 2013 incident, the IT Security Office has been encouraging multi-factor authentication sign-ups across campus. The first people required to register were employees at Duke Health, followed by faculty and staff in other departments. The push for student sign-ups began in March.
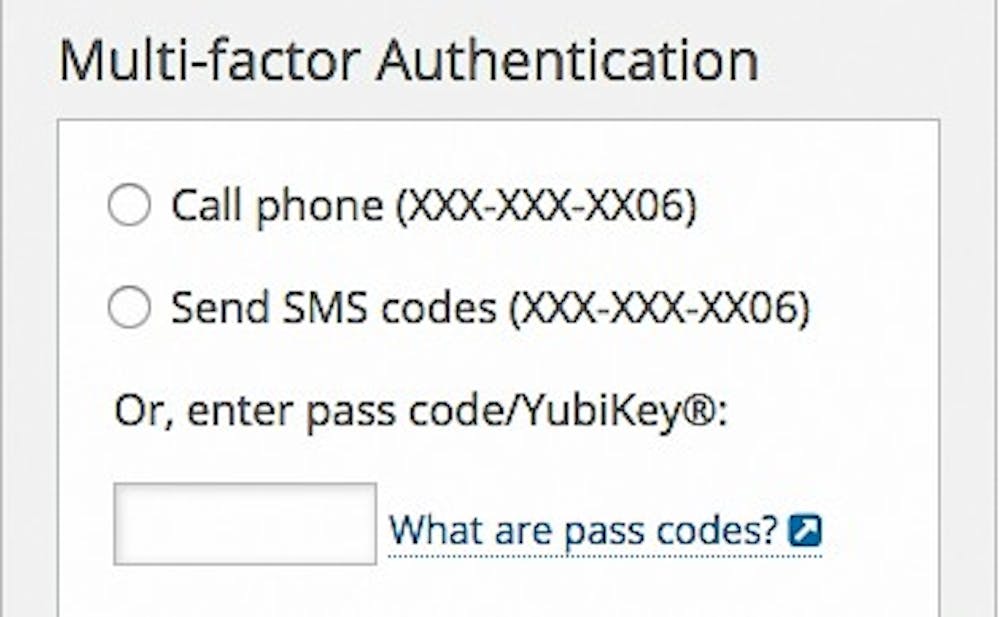
The multi-factor authentication process works in several different ways, Biever explained. Using a mobile phone or tablet, students, faculty and staff can confirm their identity via a push notification, a text message or a phone call. There is also an option for students when they do not have an internet connection or network access, as well a hardware token that can be plugged in the side of a computer for students who do not have a mobile phone or tablet.
Several students expressed frustration with the new system, which adds a few seconds to the login process.
“It seems like they are fixing what isn’t broken,” said senior Meredith Cash.
But other students said they appreciate the added layer of security. Sophomore Justin Sherman called multi-factor authentication a “cybersecurity staple” and said its implementation was necessary and overdue.
“Multi-factor authentication makes us all safer at only a marginal personal cost,” he wrote in an email. “[It] might add some additional cost or time investment in the moment, but it’s worth it in the long run.”
Junior Alexandra Fisher, who is writing her thesis about cybersecurity, noted that “people generally undervalue cybersecurity,” adding that “people don’t care about privacy until” their personal information or accounts have already been compromised. She said the slight inconvenience is outweighed by the net benefit.
Biever also said the nuisance is worthwhile.
“I realize that people feel this is a pain,” he said. “When we launched this for faculty and staff, we got similar concerns, but what I would note is that we are talking about adding three to five seconds at most to log in...This is about providing tools to our students to protect their accounts so they don’t have to worry about attackers hacking them.”
Get The Chronicle straight to your inbox
Signup for our weekly newsletter. Cancel at any time.